LDAP (the Lightweight Directory Access Protocol) is used for accessing centralized directory services. This helps reduce the effort required to manage user accounts as they can be accessed by multiple applications. One such LDAP server is Active Directory. LDAP is often used to achieve Single Sign On which allows a user to access multiple applications after logging in once.
User accounts can be synchronized between the customer LDAP server and CubeDrive, with LDAP account details being saved in the CubeDrive repository. This allows the accounts to be assigned to CubeDrive groups for allocating the required permissions and privileges for the files.
CubeDrive uses LDAP authentication to authenticate such users, with credentials being passed to the LDAP server for validation, which is required before allowing access to CubeDrive. To improve performance, successfully validated credentials can be cached by CubeDrive; with an expiry timeout to ensure that revalidation does occur after an appropriate period.
Use of such accounts is transparent to your users, they see no difference between user and group accounts created from LDAP and those created solely in CubeDrive.
LDAP authentication occurs at the repository level, so is enabled and configured by CubeDrive:
After you login CubeDrive as the system administrator, you can setup the following parameters about your LDAP. See the following image for more detail information.
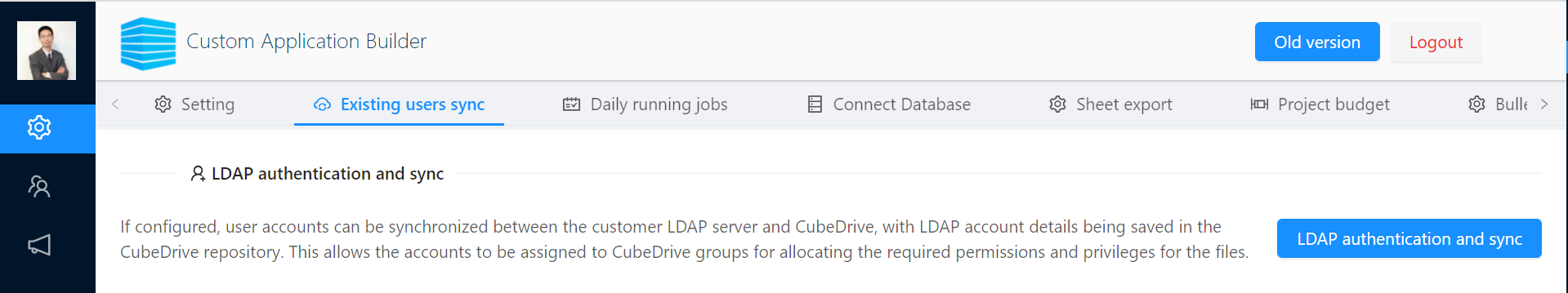 Tip: You can click "LDAP authentication and sync" to see detail under the Existing users sync tab.
Tip: You can click "LDAP authentication and sync" to see detail under the Existing users sync tab.
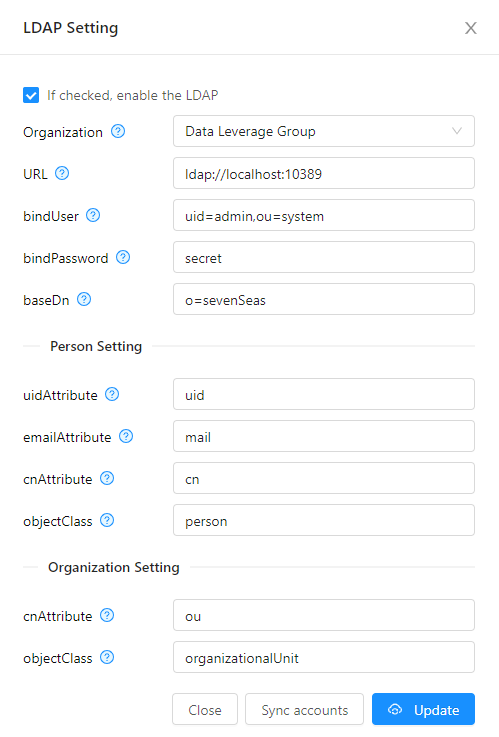
In the CubeDrive system, all the parameters about LDAP need to be setup with the following properties.
| Property | Example | Description |
|---|---|---|
| Enable | Checked | Once checked, system will enable the LDAP connection. |
| Organization | The existing organization in the CubeDrive system | Before client can sync LDAP users to the CubeDrive, client need have an existing organization to map the LDAP users. After synced, all users will be added to the mapped organization. |
| URL | $protocol :// $ldaphost : $port | This is the client URL of the LDAP service. For example: ldap://localhost:10389 |
| bindUser | Username to connect to the LDAP server. | Bind operations are used to authenticate clients (and the users or applications behind them) to the directory server. |
| bindPasword | Password to connect to the LDAP server. | It is the password to access client LDAP system. |
| baseDN | ou=People,dc=example,dc=com dc=IAIServer2, dc=local |
The Base DN is the starting point an LDAP server uses when searching for users authentication within your Directory. It is a comma-separated list of attribute and value pairs that define the User Distinguished Name (DN). The first pair must be set to " $attribute_name ={0}" indicating that the $attribute_name is equal to the user token parsed from the request. |
LDAP user need to be mapped to the CubeDrive user. The following is the LDAP person setting. When client added a user to the LDAP, in general, it includes the properties such as: uid, email, cn, object etc.
 Tip: The object classes are defined in the LDAP directory schema - they constitute a class hierarchy there, there is one central top level class (which is called 'top'), all other classes are derived from that.
Tip: The object classes are defined in the LDAP directory schema - they constitute a class hierarchy there, there is one central top level class (which is called 'top'), all other classes are derived from that.
| Property | Example | Description |
|---|---|---|
| uidAttribute | uid | [Required] User ID. This is the unique uid in the LDAP, it will be mapped to the CubeDrive user username. |
| emailAttribute | [Required] Email Address. This is the email address in the LDAP, it will be mapped to the CubeDrive user email. | |
| cnAttribute | cn | [Required] Full Name. This is the user Full Name in the LDAP, it will be mapped to the CubeDrive user firstname and last name. |
| objectClass | person | [Required] object name for person. In LDAP, an object class defines the collection of attributes that can be used to define an entry. |
The organizational unit attribute refers to the organizational unit (or sometimes the user group) that the user is part of. This will be used for mapping the organization/sub organization in the CubeDrive.
| Property | Example | Description |
|---|---|---|
| cnAttribute | ou | [Required] organization name. |
| objectClass | organizationalUnit | [Required] object name for organization. In LDAP, an object class defines the collection of attributes that can be used to define an entry. |
After client setup the above properties and click "Update" button. LDAP is ready for use. And client user can login CubeDrive with the existing accounts in the LDAP.
Tip: Client need click "Sync accounts" to load all the users from LDAP into the CubeDrive system.